Over-the-Horizon Weapons: Current and Future Trends

Over-the-Horizon (OTH) weapons systems have quietly become one of the most transformative developments in modern military technology. These systems allow nations to strike targets far beyond the visible horizon, overcoming the natural limitations imposed by the Earth’s curvature and terrain. By combining advanced sensors, long-range propulsion, and cutting-edge guidance systems, OTH weapons have reshaped how countries think about power projection, deterrence, and even the very nature of warfare. In this article, we’ll take a closer look at where these systems stand today, highlight some key examples, and explore what the future might hold for this rapidly evolving field.
The most common challenges when introducing AI to CyberSecurity
Introducing AI into cybersecurity holds immense promise, yet it comes with significant challenges that often mirror the complexity of the field itself. These challenges aren’t just technical hurdles; they extend into organizational, operational, and strategic realms, making the implementation of AI a nuanced endeavor.
The threat of “harvest now, decrypt later” attacks
The notion of “harvest now, decrypt later” attacks has emerged as a critical concern in the domain of cybersecurity, particularly in light of the anticipated development of quantum computing—a milestone commonly referred to as Q-Day. To appreciate the full ramifications of these attacks, it is essential to understand the profound impact quantum computing is expected […]
Warning of Cryptocurrency Token Impersonation Scam

Warning to the braider audience about criminals creating cryptocurrency tokens that impersonate well-known tokens, such as Tether (USDT) and other stablecoins
7 tips for cybersecurity at home or home office work

7 tips for proactively limiting or even blocking cyber threats at home to protect your home office work, your private internet activities and your children
How to compile a Suspicious Activity Report (SAR)
The way SARs are handled are often riddled with basic errors. Elements such as narrative, keywords, objective, and timing of submission can make a real difference in the quality of the reports. So how to compile an effective and correct SAR?
Guest Article, Thomas J. Dover, Ph.D., FBI
Using Research for Investigative Decision-Making
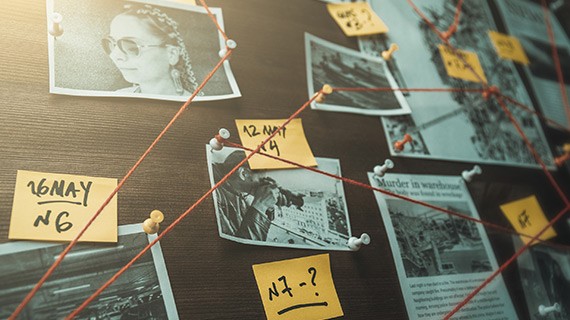
When using research to help inform decisions during investigations, decision makers must understand its legitimate use and limitations.
Correlating websites hosted on the same Cloudflare account

Cloudflare has been an asset to cyber crime organizations due to their ability to hide IP addresses using their reverse proxy service, however it can also be an asset for researchers trying to investigate these organizations by correlating different websites hosted under their ownership
Investigation and seizure of digital currency in criminal cases.
In this article we want to analyze the international and national legal regulation of the digital currencies circulation at the present stage, to assess the state of crime with the illegal use of these assets, to identify the features of the investigating such crimes and to substantiate proposals aimed at improving legislation and law enforcement […]
Fast Track to verify Email addresses

The capability to verify email addresses / accounts by username is often time-consuming. In this article we introduce a very effective tool.


