The notion of “harvest now, decrypt later” attacks has emerged as a critical concern in the domain of cybersecurity, particularly in light of the anticipated development of quantum computing—a milestone commonly referred to as Q-Day. To appreciate the full ramifications of these attacks, it is essential to understand the profound impact quantum computing is expected to have on cryptographic security.
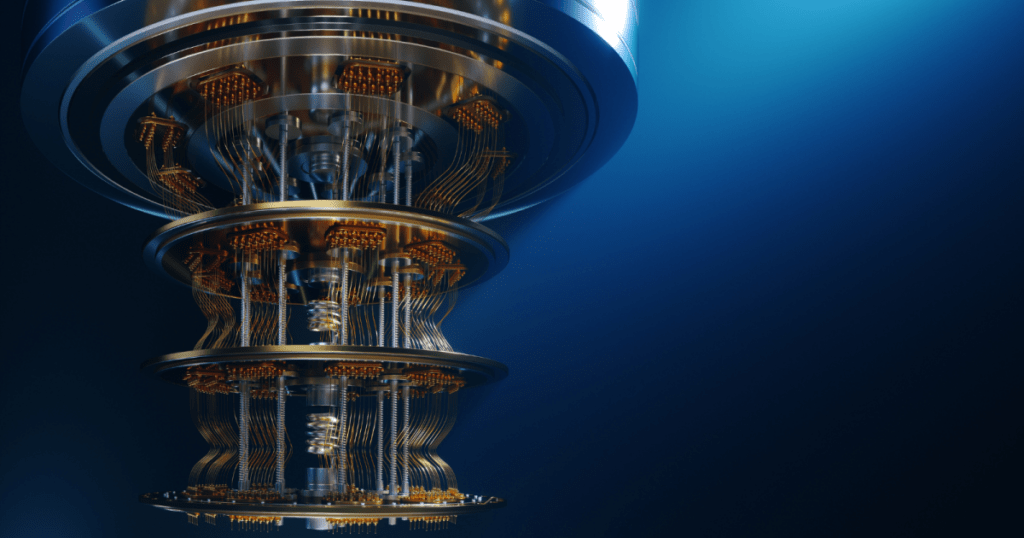
Quantum computing, leveraging the principles of quantum mechanics, promises to perform complex computations at unprecedented speeds, thereby revolutionizing numerous fields. While the potential benefits are substantial, this technology poses a significant threat to contemporary cryptographic methods. Many widely-employed encryption techniques, including RSA (Rivest–Shamir–Adleman) and ECC (Elliptic Curve Cryptography), rely on the inherent difficulty of factoring large integers or solving discrete logarithms—tasks that quantum computers could potentially accomplish with relative ease using algorithms such as Shor’s algorithm.
The risk of “harvest now, decrypt later” attacks arises within this context. These attacks involve adversaries intercepting and storing encrypted data with the intention of decrypting it in the future, when quantum computers are capable of breaking current encryption standards. The implications are severe: data that is deemed secure today could become susceptible to exposure once quantum decryption capabilities are realized. This encompasses a vast array of sensitive information, from personal and financial data to state secrets and proprietary corporate information.
The timeline for Q-Day, the hypothetical day when a quantum computer capable of breaking modern cryptographic protocols becomes operational, remains indeterminate. Some experts predict this could occur within the next decade, while others estimate it may take several decades. Despite this uncertainty, the risk of future decryption necessitates immediate action to address potential vulnerabilities. The rationale is straightforward: intercepted data today may retain its value and sensitivity for many years, thereby posing significant risks if decrypted in the future.
In response to these risks, the cybersecurity community advocates for a transition to quantum-resistant cryptography. This entails developing and deploying new cryptographic algorithms that are secure against both classical and quantum attacks. The National Institute of Standards and Technology (NIST) has been leading this effort, conducting a rigorous competition to identify and standardize post-quantum cryptographic algorithms. This selection process ensures that the chosen algorithms provide robust security and practical performance.
However, transitioning to quantum-resistant cryptography presents numerous challenges. Updating global digital infrastructure with new cryptographic standards is a complex and resource-intensive endeavor. It requires updating hardware and software, ensuring compatibility, and educating stakeholders about the new protocols. Moreover, there is an inherent risk during the transition period: as organizations adopt quantum-resistant algorithms, they must maintain the integrity and security of existing systems, which remain vulnerable to future quantum decryption.
In addition to technological solutions, policy and regulatory measures are crucial in preparing for Q-Day. Governments and international bodies must collaborate to establish guidelines and best practices for managing the transition to quantum-safe cryptography. This includes funding research initiatives, supporting public-private partnerships, and prioritizing critical infrastructure sectors in the migration process.
The threat of “harvest now, decrypt later” attacks underscores the necessity of a proactive approach in cybersecurity. By anticipating the capabilities of future quantum computers, it is possible to take measures today to protect sensitive data against potential vulnerabilities. The transition to quantum-resistant cryptography is a complex yet indispensable task, requiring coordinated efforts across technology, policy, and education. While the exact timing of Q-Day remains uncertain, the imperative to act is unequivocal: the security of our digital future is at stake.